Your First 30 Days: A No-Drama Data Migration Plan with Legal Software
A phased 30-day plan for legal software data migration allows your firm to move systems without interrupting billing or losing critical...

What Is Legal Process Automation? How to Use It to Streamline Your Workflows
Legal process automation allows growing firms to automate non-billable work and focus more time on tasks that land on an invoice.

Lawyer Billing Models, Explained: Which One Fits Your Firm?
In this guide, we’ll break down the most common law firm billing methods and show how modern technology helps protect profitability.

How to Resolve Unhappy Client Situations: Effective Strategies for Lawyers
When you resolve unhappy legal clients using a consistent framework, you can protect trust and strengthen a fragile relationship.

How to Grow a Law Firm. A Practical Guide for Sustainable Success.
Growing a law firm is rarely about doing one big thing. It is about making smarter decisions across marketing, operations, finances,...
Law Firm Credit Card Guide: Rules, Fees, and Smart Setup
Accepting credit cards can improve cash flow, but law firms must follow strict ethical rules. This law firm credit card guide...
The intuitive design and robust features of CosmoLex have been a game-changer for my firm. I recommend it to any solo practitioner looking to reclaim their time.

Jonathan Roth
Founder, Roth Advocacy
Canada
Customer Centric Messaging
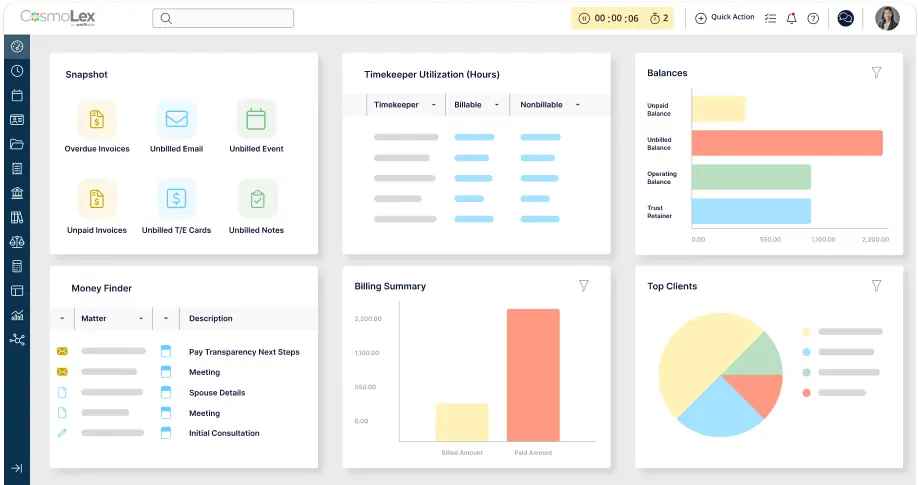
Cosmolex provides a familiar and simple user interface that allows our firm to quickly and efficiently manage billing and times.

Law Firms and the Cloud: The Real Pros, Cons, and Payoff
At some point, every firm hits the same crossroads: outdated software vs. the cloud. This guide separates hype from reality, covering...

A Practical Playbook for Running a Remote Law Firm
Running a remote law firm requires more than just working from home. Discover the essential infrastructure, security safeguards, and automated workflows...

Are Accounts Receivable an Asset?
Attorney billing increments help firms track time consistently, but they can also create manual work and errors. Learn the most common...

Attorney Billing Increments: Which One Fits Your Firm?
Choosing the right billing increments helps firms track time in a fair, consistent way while keeping invoices accurate and easy to...
What Is the Difference Between a Flat Fee Agreement and a Retainer for Law Firm Pricing?
What’s the difference between a flat fee agreement vs retainer? Learn when to use each model to optimize your law firm’s...

Law Firm Accounting Guide: What You Need to Know About Handling Client Funds
This law firm accounting guide walks you through the core areas of legal accounting to manage client funds confidently, stay compliant...

What Are the Most Common Ethics Violations for Lawyers?
What are the common ethics violations for lawyers? We break down the most frequent risks—from conflicts of interest to trust accounting...

How Much Should Your Law Firm Bill for Paralegal Work?
Law firms can bill paralegal work at market rates, increasing firm profitability. Learn how to determine the right paralegal billing rate...

What Forms of Payment Do Lawyers Accept?
If you’re hiring a lawyer, you have options for payment! Learn about the most common lawyer payment methods, from credit cards...
Sign up for weekly tips and news from CosmoLex.
Simplify your practice with one tool.
Book a demo.
Book a personalized demo with a CosmoLex specialist and see the platform in action.